Your cyber program should produce decisions, not just findings.
We deliver consulting, tools, and training that turn cybersecurity into clear, defensible decisions — from assessment through governance and test planning.
Most cyber programs produce findings, not decisions. Assessments list what is wrong — but not what it costs the mission, which to fix first, or how much to spend. Risk owners are left to defend budgets they cannot explain and priorities they cannot prove.
How We Work With You
We deliver the service
Cyber GRC consulting and execution: we assess, prioritize, and deliver decision artifacts your team can act on.
Your team runs it
We provide tools that make GRC management faster and more effective, with guided support.
Tools + training
We provide the tools and training to help you build and manage your own cybersecurity program.
What We Deliver
Cyber Risk Assessment Tools and Services
Independent, mission-based cyber risk assessment with ranked risks, mitigation options, and budget recommendations.
See risk assessment →Risk Management Tools and Services
Governance support and tooling to track decisions, owners, timelines, and risk reduction progress.
See risk management →Cyber T&E Tools and Services
Validate implementations and controls with evidence — for programs that require proof of effectiveness.
See cyber T&E →The cybersecurity process you should be following
We provide consulting across all stages — with dedicated services and products where highlighted.
Define, Govern, Identify
Mission context, ownership, assets, and threats — the foundation for every risk decision that follows.
Stages 1–3Foundational Advisory
We provide consulting across these foundational stages — defining mission context, establishing governance, and identifying critical assets and threats.
Assess Risk
Pain: priorities are guesswork. Outcome: ranked risk register with consequence × likelihood scoring.
query_stats Focus AreaCORA Service
Mission-based cyber risk assessment producing ranked risks, mitigation options, and leadership briefs.
See full service detail →Plan Treatment
Pain: risk data lacks decisions. Outcome: risk decision records with mitigation options and budget context.
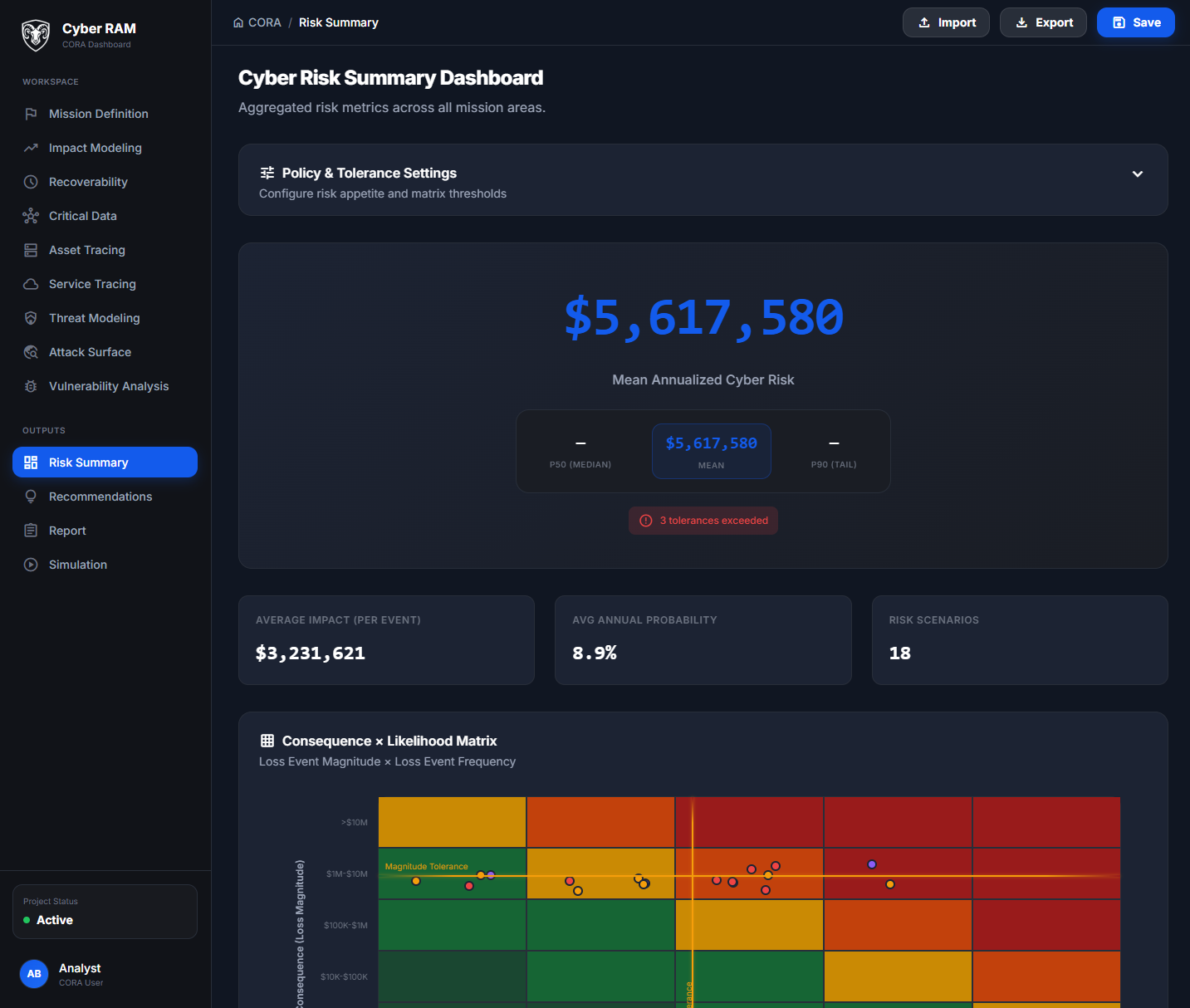
edit_note Focus AreaCORA Platform
Dashboard to model treatment options, track decisions, and produce leadership-ready artifacts.
Explore CORA →Select Controls & Implement
Control strategy and deployment — translating risk decisions into protective measures across your environment.
Stages 6–7Implementation Support
Control selection guidance and implementation support — ensuring chosen mitigations align with risk priorities and budget.
Test & Validate
Pain: no proof controls work. Outcome: evidence packages and structured cyber test plans.
published_with_changes Focus AreaCyber T&E
Structured test planning and evidence templates that prove your controls work as intended.
Learn about Cyber T&E →Risk Management
Pain: decisions not tracked to closure. Outcome: governance cadence and progress reporting.
monitoring Focus AreaRisk Management Service
Ongoing governance: decision tracking, roadmap visibility, and risk reduction metrics for leadership.
Risk management details →Report, Improve, Re‑assess
Leadership reporting and continuous improvement — closing the loop with posture dashboards and trend analysis.
Stages 10–12CORA Platform
Posture dashboards, trend reporting, and re-assessment workflows that feed the next cycle.
Explore CORA →Where Do You Start?
Start with a cyber risk assessment — ranked risks, mitigation options, and budget recommendations.
Book a scoping call →MBCRA and Cyber T&E services for acquisition lifecycle and RMF support.
See government & defense →See the CORA dashboard — decision-grade risk assessment in one screen.
Explore CORA →Our Approach
We are not your MSP or your tool vendor. We report to the risk owner.
Every deliverable is built for a decision: budget, priority, or governance.
We show our work. Confidence levels, constraints, and caveats included.
Air-gap and limited data movement support scoped during kickoff.
Ready to get a clear risk picture?
Book a scoping call. We'll discuss your environment and define the right scope.
Book a Scoping Call